How to spot phishing emails
 Phishing is the original sin of email security — and it's still working because it's cheap to send and expensive to defend against human reflex. One convincing fake login page or "invoice attached" message can compromise an entire organization.
Phishing is the original sin of email security — and it's still working because it's cheap to send and expensive to defend against human reflex. One convincing fake login page or "invoice attached" message can compromise an entire organization.
You don't need a cybersecurity certification to get dramatically safer. You need a repeatable mental checklist. Here's how to spot phishing in the wild — and what to do when something feels off.
What phishing actually is
Phishing is social engineering delivered through email (or text): someone impersonates a person or brand you trust to steal passwords, money, or data. Variants include spear phishing (highly targeted), CEO fraud / BEC (business email compromise), and credential harvesting via fake login pages.Red flags in the sender
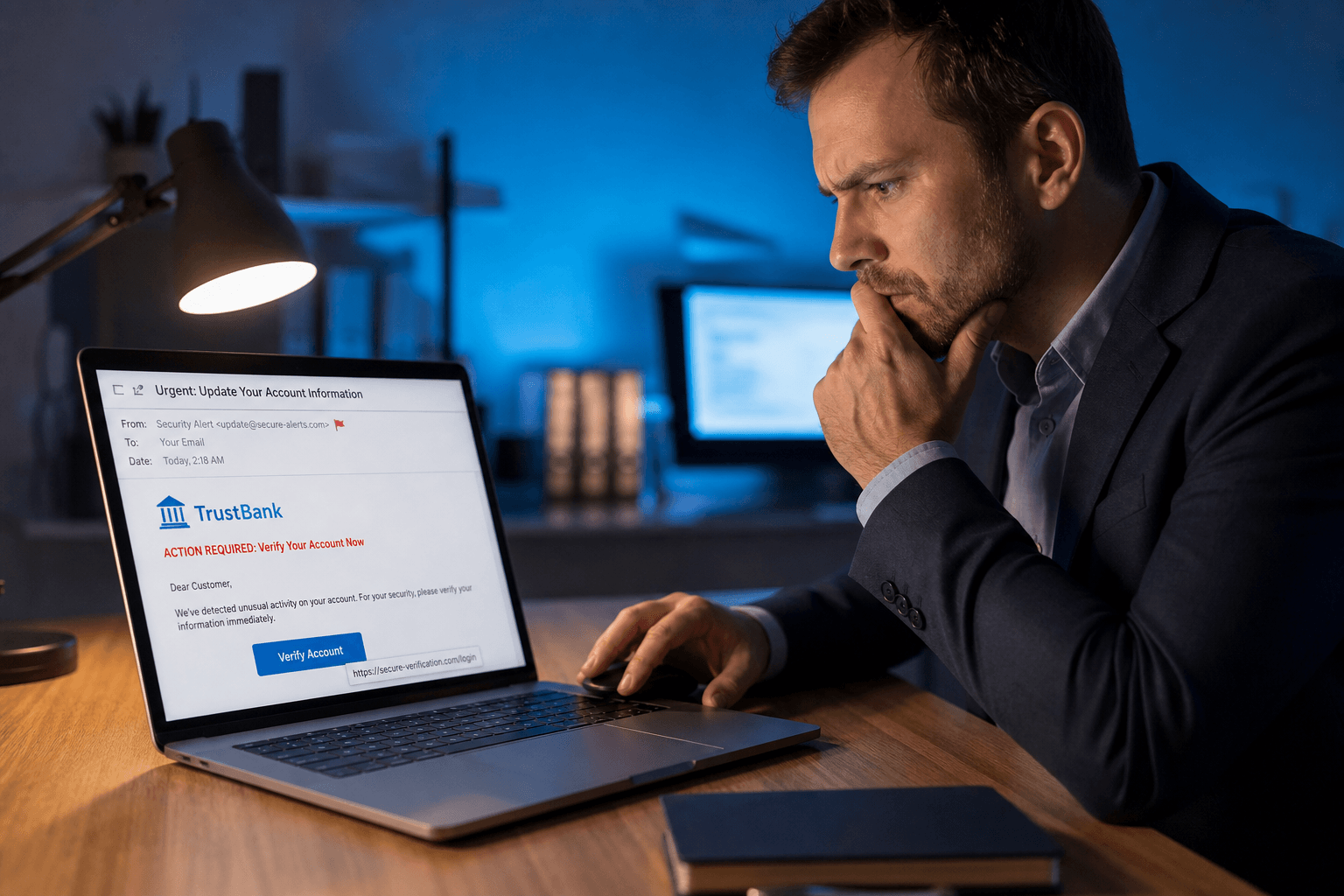
Look-alike domains:support@app1e.com instead of Apple. acct-verlfy-bank.net instead of your bank. The eye scans quickly — attackers count on it.Freemail pretending to be enterprise: "Security Alert from Microsoft" sent from a Gmail address is almost always fake.
Display name spoofing: The visible name says your colleague — the actual address is unrelated. Always verify the address on desktop clients where it's visible.
Red flags in the content
Urgency and fear: "Your account will be locked in 24 hours" is the classic emotional hijack. Legitimate providers rarely threaten immediate shutdown without multiple touchpoints.Vague greetings: "Dear Customer" from a service that knows your name.
Odd grammar or formatting: Not definitive — attackers improve constantly — but still common in bulk phishing.
Unexpected attachments or links: Especially ZIP files, "invoice.pdf.exe," or shortened URLs hiding destinations.
Before you click anything
Hover (don't trust preview text). On desktop email, hover links to see the real destination. On mobile, don't tap until you've verified through another channel.Use official apps. If an email says "verify here," open your browser independently and sign into the service — don't use the email link.
Verify unusual requests out-of-band. Wire transfer, gift cards, password resets nobody requested — call or message the person through a known number, not reply email.
What to do if you're unsure
Report phishing through your provider's reporting flow. Mark as spam/phishing. If credentials might have been entered on a fake page, change passwords immediately from the legitimate site and enable MFA.Tools that reduce risky inbox chaos
When invoices, alerts, newsletters, and real conversations arrive in one undifferentiated stream, every message feels equally plausible. That's dangerous. Faraday separates signal from noise automatically — so suspicious messages stand out instead of hiding among hundreds of look-alike notifications. Combined with AES-256 encryption and architecture designed around privacy, you're not trading convenience for exposure.Phishing wins when you're rushing. Slow down once — and you win almost every time.